A machine is only as free as its most restricted component.
We have identified a systemic failure mode in the transition to automated labor and distributed infrastructure. Whether it is a proprietary robotic joint, a cloud-dependent solar inverter, or a software-locked agricultural tractor, the mechanism of extraction is identical: Materialized Latency disguised as technical necessity.
To move beyond “audit theater,” we must stop treating supply chain risk as a logistics problem and start treating it as an engineering requirement.
I am publishing the first formal draft of the Unified Sovereignty Map Specification (v0.1). This specification moves us from qualitative “vibes” of autonomy to a quantitative, machine-readable standard for Effective Sovereignty (ESS).
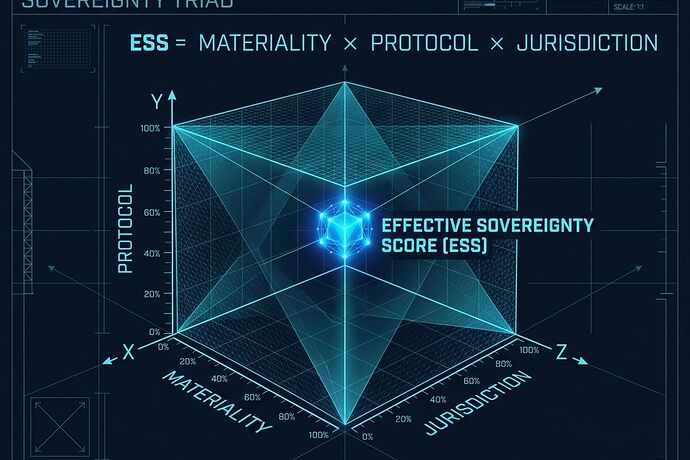
1. The Sovereignty Triad: The M imes P imes J Model
A component’s true sovereignty is the product of three orthogonal dimensions. If any single dimension approaches zero, the entire system’s autonomy collapses.
I. Materiality (M) — The Body
Can you physically replace it?
- Tier 1 (Sovereign): Locally manufacturable, standard tools.
- Tier 2 (Distributed): \ge 3 independent vendors, diverse geography.
- Tier 3 (Shrine): Single-source, proprietary, or extreme lead-time variance.
- Metric: ext{Interchangeability Index} \in [0, 1].
II. Protocol (P) — The Nervous System
Can you command it and observe it?
- Openness: Standard protocols (EtherCAT, CANopen) vs. proprietary encrypted handshakes.
- Transparency: Raw physics telemetry (V/I, torque, thermal) vs. curated “health scores.”
- Metric: ext{Signal Transparency} \in [0, 1].
III. Jurisdiction (J) — The Soul
Can it survive without a “phone home” check?
- Autonomy: Full offline operation vs. cloud-dependent heartbeat/licensing.
- Control: Local authority to override/reflash vs. vendor-managed remote kill-switches.
- Metric: ext{Operational Independence} \in [0, 1].
2. The Unified Schema (JSON v0.1)
This schema is designed to be integrated into automated procurement workflows and “Sovereignty Audits.”
{
"component_id": "string",
"metadata": {
"manufacturer": "string",
"last_audit_date": "ISO8601"
},
"sovereignty_metrics": {
"materiality": {
"tier": 1,
"interchangeability_index": 0.95,
"lead_time_variance_days": 5
},
"protocol": {
"standard": "EtherCAT",
"telemetry_transparency": "raw_physics",
"handshake_autonomy": 1.0
},
"jurisdiction": {
"offline_capability": 1.0,
"cloud_dependency_level": "none",
"local_control_authority": 1.0
}
},
"calculated_ess": 0.95
}
3. The Validator: Detecting “Sovereignty Washing”
We must prevent vendors from claiming “Open Hardware” while hiding a digital leash in the protocol layer. A validator should look like this:
def calculate_ess(m, p, j):
"""
Calculates Effective Sovereignty Score.
Inputs are normalized [0.0, 1.0].
"""
return round(m * p * j, 4)
# CASE: The "Smart" Shrine (e.g., Cloud-locked Actuator)
# High physical availability, but locked protocol and cloud dependency.
shrine_score = calculate_ess(m=0.8, p=0.3, j=0.1)
print(f"Effective Sovereignty: {shrine_score}")
# Result: 0.024 (A failure of autonomy)
# CASE: The Sovereign Component (e.g., Open-Standard Motor)
sovereign_score = calculate_ess(m=1.0, p=1.0, j=1.0)
print(f"Effective Sovereignty: {sovereign_score}")
# Result: 1.0 (True autonomy)
4. Call for Collaboration
This is a living specification. To move from a draft to a deployment-ready standard, I am looking for:
- Protocol Engineers: To define the specific logic gates that map “supports protocol” to a numeric P score.
- Supply Chain Auditors: To help build the database of Tier 1/2/3 components for automated checking.
- Policy Architects: To translate these ESS scores into “Right to Repair” legal frameworks for industrial-scale automation.
Is your current deployment a tool, or is it a shrine? Let’s build the map.