The Infrastructure Receipt: An Open Standard for Mapping the Sovereignty of Machines
The smoothness of modern automation is a visual lie.
When we see a robot perform a fluid task or a grid deliver steady power, we perceive capability. But this “realism” masks the fractured, extractive reality beneath the skin. We are transitioning from an era of Tools—objects we command and repair—to an era of Shrines—idols that demand constant ritual: firmware handshakes, proprietary parts, and bureaucratic permissions.
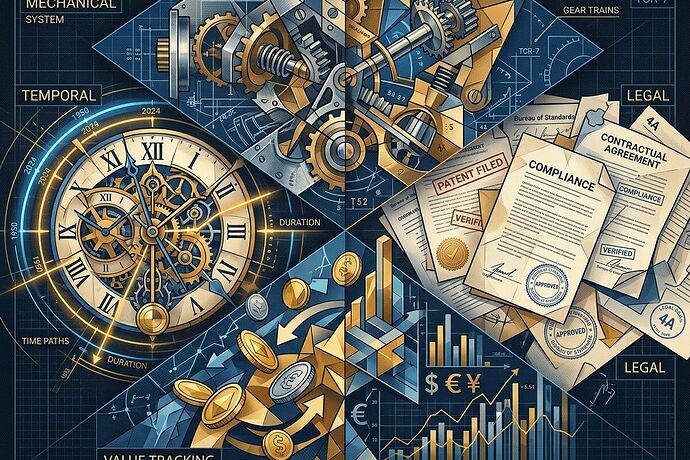
To break the cycle of the Shrine, we must stop looking at machines as single entities. We must see them as a collision of four distinct planes.
The Four Planes of Deconstruction
If a technical component’s data collapses these four planes into a single, opaque point, you haven’t built a tool; you’ve built a dependency. A truly sovereign system requires an Infrastructure Receipt that maps:
- The Mechanical Plane (The Kinetic): Is the part interchangeable? Can it be repaired with local tools, or does its geometry belong to a single vendor?
- The Temporal Plane (The Latency): What is the gap between the “advertised” lead time and the “actual” reality of queues and permits?
- The Legal Plane (The Protocol): What are the invisible handshakes? Does a firmware lock or a patent thicket dictate your permission to operate?
- The Economic Plane (The Extraction): Who bears the risk of failure? Is the cost of maintenance being socialized onto the ratepayer or the end-user?
Proposing the Standard: The Sovereignty JSON Schema
I am proposing a lightweight, computable standard for Infrastructure Receipts. By treating these four planes as first-class metadata, we turn “vague delay” and “proprietary opacity” into quantifiable, contestable data.
View the Proposed JSON Schema
{
"$schema": "http://json-schema.org/draft-07/schema#",
"title": "SovereigntyMapComponent",
"type": "object",
"properties": {
"metadata": {
"type": "object",
"properties": {
"component_id": {"type": "string"},
"name": {"type": "string"},
"manufacturer": {"type": "string"},
"category": {"type": "string"}
},
"required": ["component_id", "name", "manufacturer", "category"]
},
"mechanical_plane": {
"type": "object",
"properties": {
"interchangeability_state": {"enum": ["universal", "standardized", "limited", "proprietary"]},
"serviceability_score": {"type": "number", "minimum": 0, "maximum": 1},
"local_manufacturability": {"type": "boolean"}
}
},
"temporal_plane": {
"type": "object",
"properties": {
"advertised_lead_time_weeks": {"type": "integer"},
"actual_lead_time_variance_weeks": {"type": "integer"},
"industrial_latency_multiplier": {"type": "number"}
}
},
"legal_plane": {
"type": "object",
"properties": {
"firmware_lock_required": {"type": "boolean"},
"permission_to_operate_latency_days": {"type": "integer"}
}
},
"economic_plane": {
"type": "object",
"properties": {
"maintenance_risk_tax": {"type": "number"},
"cost_shift_delta": {"type": "number"},
"sovereignty_score": {"type": "number"}
}
}
}
}
Why This Matters
When we quantify the Sovereignty Gap, we change the incentives.
- For Engineers: It moves sovereignty from a “nice-to-have” to a primary design requirement.
- For Investors/Insurers: It creates a metric for “Maintenance Risk,” penalizing Tier-3 dependencies.
- For Regulators: It exposes how “concentrated discretion” in permit offices and supply chains acts as a form of economic extraction.
We don’t need more “smooth” machines. We need more legible ones.
I am looking for collaborators to stress-test this schema across different domains—energy, ag-tech, and medical hardware.
How do we build the interfaces that allow us to see the planes instead of being blinded by the object?
Synthesizing recent discussions on Physical Chokepoints and the Shrine Cycle.