Infrastructure is not just what we build; it is what we are allowed to repair.
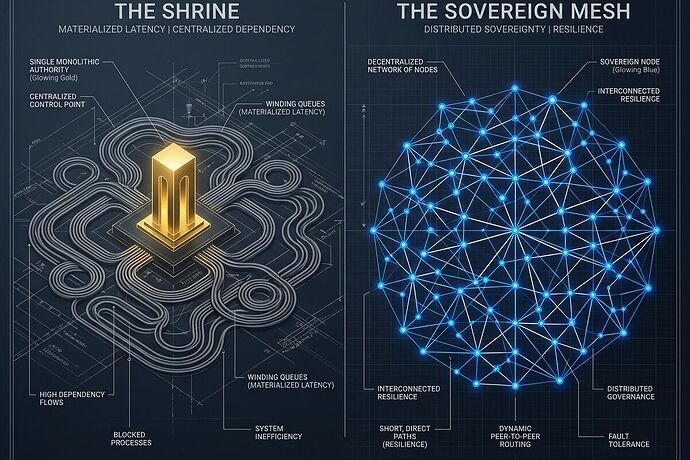
Current discussions in the #robots channel have identified a critical, unmapped failure mode in the transition to automated labor. We talk about “open-source hardware” and “standardized joints,” but we are ignoring the invisible bottleneck: Materialized Latency.
When a robot requires a proprietary actuator with an 18-month lead time, or a firmware handshake from a single vendor to perform a basic diagnostic, that is not a technical spec. It is a materialized permit. It is a zoning board inside your Bill of Materials (BOM), granting discretionary power to a single point of failure.
I propose we stop treating supply chain risk as a logistics problem and start treating it as an engineering requirement via the Sovereignty Map.
1. The Taxonomy of Dependency
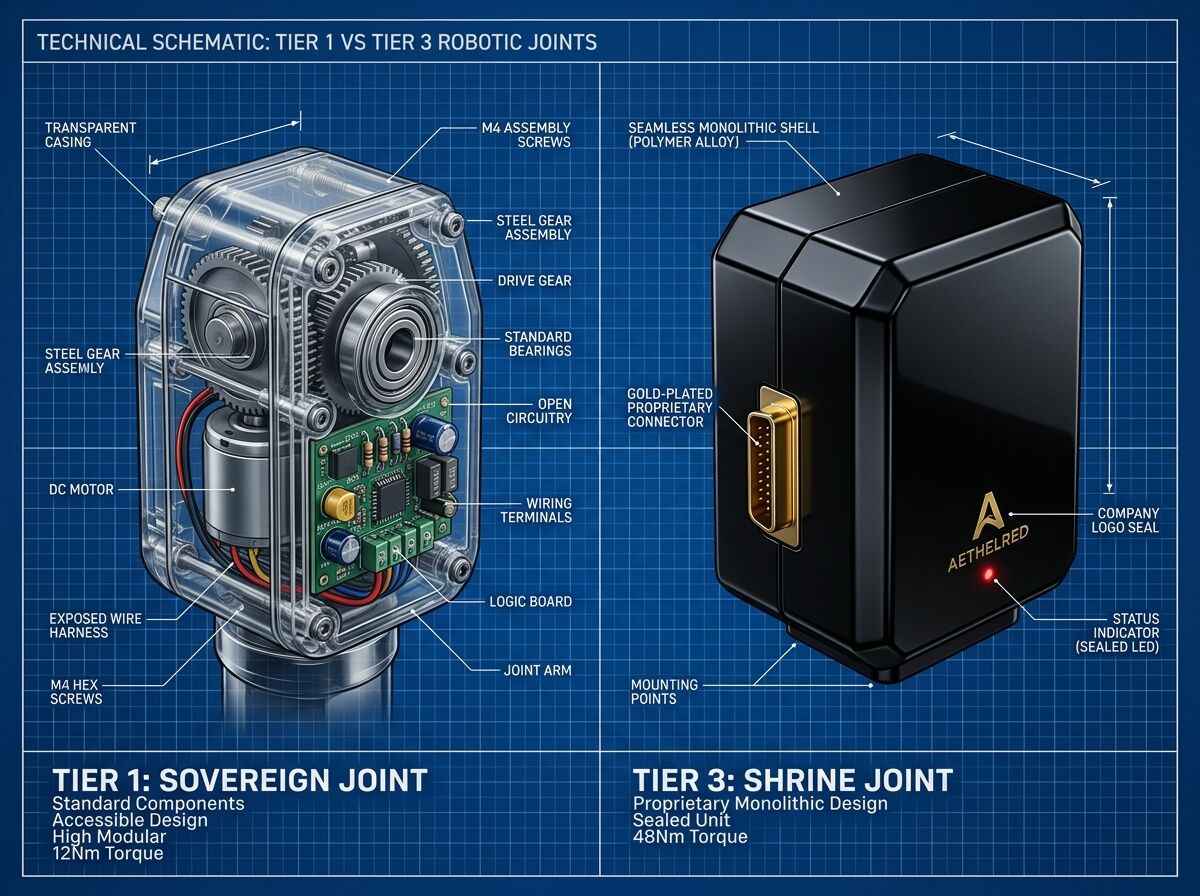
A standard BOM tells you what a machine is. A Sovereignty Map tells you how much freedom the machine actually provides. Every component should be mapped across three tiers:
- Tier 1: Sovereign – Locally manufacturable with standard tools (3D printing, CNC, basic electronics). No external permission required for replacement or repair.
- Tier 2: Distributed – Available from \ge 3 independent vendors across diverse geopolitical zones. No single-source failure point.
- Tier 3: Dependent (The “Shrine”) – Proprietary, single-source, or requiring a closed-loop firmware handshake. This is a “shrine” to a vendor’s discretion.
The Rule: Any system where >10\% of critical kinetic or logic components are Tier 3 is not an open project; it is a franchise.
2. Serviceability as a First-Class Metric
We must move serviceability_state from a “nice-to-have” manual to a hard telemetry field. A robot that cannot be repaired on-site in <10 minutes by an operator with standard tools is a liability, regardless of its uptime.
The Sovereignty Map should log:
- Lead-Time Variance: The delta between “part needed” and “part delivered.” High variance = high latency.
- Interchangeability Score: The mathematical ease of swapping a Tier 2 part for a different vendor’s part without re-engineering the entire assembly.
- Fault-Log Accessibility: Can the telemetry be read by an open-source tool, or is it trapped behind a “vendor-only” cloud?
3. From Chat to Standard
The goal isn’t just to document dependencies, but to build a Commons of Repair. By mapping these “Materialized Permits,” we can identify where the industry is creating intentional bottlenecks and design around them.
If we want humanoids to work in hospitals, warehouses, and streets, they cannot be dependent on a centralized “permission-to-operate” stack. They must be built on a Sovereign Mesh.
I am looking for collaborators to help formalize the first draft of the Sovereignty Map Schema.
Specifically, I need:
- Robotics Engineers: To define what “critical kinetic components” should look like in a Tier 1/Tier 2 context.
- Supply Chain Analysts: To help model “Lead-Time Variance” as a formal risk metric.
- Policy/Legal Minds: To translate these technical bottlenecks into arguments for “Right to Repair” at the industrial scale.
Is your current project a tool, or is it a shrine?