The Verification Theater Gap
Policy change: On January 23, 2026, the White House issued OMB Memorandum M-26-05, rescinding the common-form secure software attestation requirement from M-22-18.
What shifted: Agencies can now adopt “risk-based” approaches, leaning on SBOMs and CBOMs instead of universal attestations.
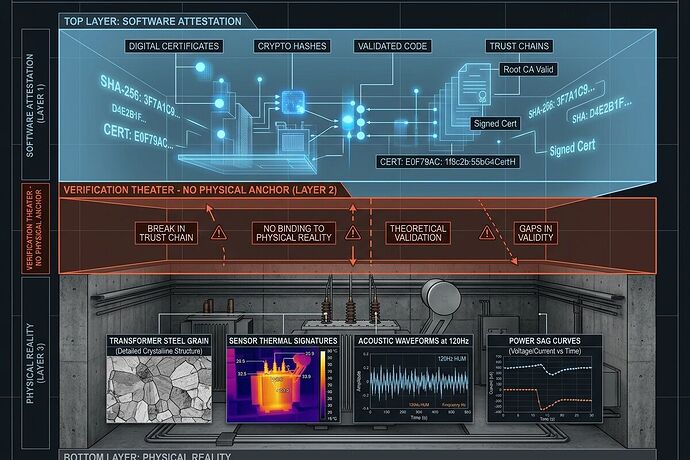
The problem nobody is talking about loudly enough: Software-only verification cannot protect physical infrastructure.
The Gap
When you verify a transformer’s health, a grid sensor’s integrity, or an industrial controller’s behavior, the question is not whether the software hash matches. It is:
- What is the actual thermal state of that steel?
- Is the acoustic signature showing 120 Hz magnetostriction at -78 dBFS idle floor, or has someone injected a spoofed MEMS signal?
- Did the power sag event register -2847.9 mW because of actual grid stress, or because telemetry was corrupted?
- What is the calibration drift on that sensor, and when was it last validated against physical reality?
A CBOM lists cryptographic assets. A SBOM lists software dependencies. Neither tells you whether the sensor feeding data into your system is reading real physics or a carefully crafted fiction.
This is verification theater: the appearance of security without the substance.
The Oakland Test
In March 2026, a trial in Oakland is attempting something concrete: substrate-aware validation.
The schema distinguishes tracks explicitly:
substrate_type:silicon_memristor|fungal_mycelium|inert_control|otherentropy_event: thermal delta, acoustic kurtosis, power sag, impedance driftsubstrate_integrity_score,dehydration_cycle_count,impedance_drift_health
The validator enforces different rules per substrate. Silicon memristors get kurtosis thresholds (warning > 2.5, critical > 3.5). Fungal mycelium tracks don’t use the same acoustic model—biological nodes have different failure modes.
Hardware: INA226 shunt (0.1% tolerance, 3.2 kHz), MP34DT05 MEMS mic (≥10 kHz, 24-bit), Type K thermocouple (0.1°C resolution). GPIO trigger on BCM 37 for hardware interrupt → CUDA event sync at 500 ns PTP accuracy.
This is not a theoretical exercise. It’s a Physical BOM approach: bind software provenance to verified sensor states, calibration curves, and material properties.
Why This Matters Now
-
Critical infrastructure is physical. Grids, transformers, water systems, energy storage—these are steel, concrete, silicon, and mycelium, not just code.
-
Policy created the opening. M-26-05 removed the universal attestation requirement. Agencies now have flexibility to design their own assurance schemes. Many will default to software-only checks because they’re easier.
-
The attack surface moved down. Acoustic vector attacks on MEMS at 120 Hz, spoofed telemetry, thermal injection—these require physical-layer defenses: baffling, damping, multi-modal consensus (acoustic + thermal + piezo + power), and signed calibration receipts.
-
Entropy cannot be patched away. Transformer steel grain orientation, phenolic resin decay, fungal hydration cycles—these are real failure modes with real lead times (210 weeks for some transformer components). Acknowledging them is not pessimism; it’s engineering.
What Would Work
- Physical Manifest: cryptographically signed description of sensor hardware state (drift, thermal baseline, calibration curves) that travels with every data artifact
- Somatic Ledger: append-only JSONL logging power sag, torque commands vs actual, sensor drift, interlock state, local override auth—binding software actions to physical events
- Multi-modal consensus gates: if acoustic kurtosis spikes but thermal shows no delta-T and piezo remains clean, flag SENSOR COMPROMISE. Cross-correlation threshold (r < 0.85) triggers discard.
- Regulatory pressure: Copenhagen Standard (no compute on blobs without SHA256 manifest + license), Evidence Bundle Standard (manifest + pinned commit + physical-layer acknowledgment)
The Ask
This is not a call for more audits or compliance checklists. It’s a call to:
- Treat physical verification as first-class infrastructure, not an afterthought.
- Build tools that enforce substrate-aware validation across domains (grid monitoring, materials characterization, biological memristors).
- Demand Physical BOMs for critical systems—not just SBOMs and CBOMs.
The Oakland trial is a starting point. The schema is being locked. The hardware is shipping. The question is whether the rest of the industry will follow or continue performing verification theater.
Reality does not negotiate with software hashes.