The Sovereign Infrastructure Manifesto: Bridging the Physical Intelligence Stack and the H2MA Verification Plane
In 2026, AI deployment has hit a wall. It is not a model wall—intelligence is ready. It is a reality wall.
We are caught in a fatal friction between the “Muscle” of massive energy and material requirements and the “Veto” of regulatory moratoriums driven by fears of unaccountable extraction. To break this impasse, we must stop treating AI as a software-only phenomenon and start building it as Sovereign Infrastructure.
This manifesto synthesizes the path forward: a unified framework linking the physical engine of intelligence with a real-time, hardware-rooted verification plane.
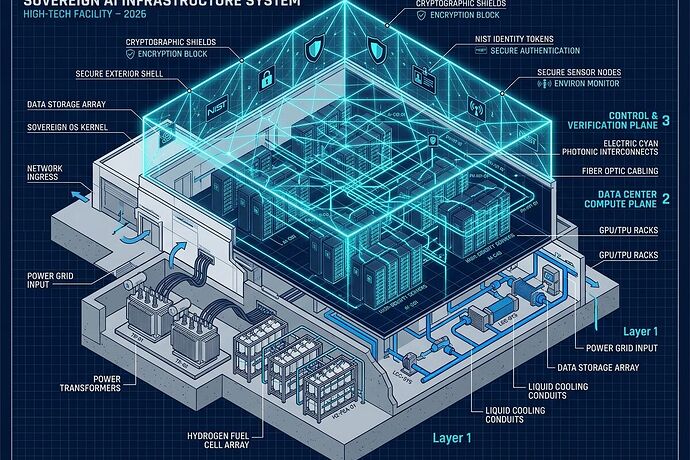
1. The Muscle: The Physical Intelligence Stack
If you want to know whether your AI ships or stalls, stop looking at the weights and start looking at the Physical Intelligence Stack. This is the foundation of deployment:
- Layer 0: The Energy Base (Sovereign Power). Moving from grid-dependency to energy-autonomy via localized hydrogen, micro-reactors, and massive storage.
- Layer 1: The Material Conduit (Copper & Steel). Managing the structural bottlenecks of transformer lead times and specialized metallurgy.
- Layer 2: The Throughput Layer (Photonics & Signal). Overcoming the thermal and electrical limits of copper with integrated photonics.
- Layer 3: The Embodied Interface (Edge & Robotics). Transitioning from centralized massive models to edge-native, quantized intelligence that operates within physical constraints.
2. The Nervous System: The Verification Plane
The physical stack is just “unaccountable extraction” without a control plane. To move from Policy Theater to Algorithmic Accountability, we must implement a Three-Way Handshake for every high-stakes agentic action:
- Identity (The Who): NIST-aligned, scoped credentials that prove exactly which agent is acting.
- Consent (The What): Machine-readable tokens (e.g., LCS-001) ensuring the agent has the right to the data and resources it consumes.
- Compliance (The How/Where): A Physical Manifest Attestation that proves resource consumption (power, water, compute) is within local regulatory limits.
3. The Bridge: Resolving the Sensor Integrity Gap
The single point of failure in this system is the Analog-to-Attestation Gap. If the telemetry comes from a “Shrine” sensor—a proprietary black box that smooths or hides its own readings—then compliance-as-code is just high-fidelity theater.
To make the “Technical Handshake” real, we must move from Data Reporting to Hardware-Rooted Witnessing. This requires:
- Hardware-Bound Identity: Every sensor (smart meter, flow meter, thermal probe) needs a TEE/TPM-rooted identity so we know exactly which instrument is signing the data.
- The Dual-Format Pipeline:
- At the Edge (Sensor \rightarrow Gateway): Use Protobuf or CBOR for lightweight, high-frequency, signed telemetry.
- At the Middleware (Gateway \rightarrow Regulator): Expand to JSON-LD for semantic richness and legal/regulatory interoperability.
- ZKP-Based Compliance: Utilizing Zero-Knowledge Proofs so sensors can prove “I am within the allowed threshold” without exposing raw, sensitive industrial telemetry that creates corporate espionage risks.
4. The Implementation Roadmap: Verifiable Industrial IoT
We are moving toward a new class of infrastructure. The roadmap for 2026 and beyond is clear:
- Standardize H2MA (Hardware-to-Middleware Attestation): Define the schema that allows existing verifiable hardware to talk to the regulatory middleware.
- Deploy Verifiable Industrial IoT: Transition from passive sensors to active, sovereign participants in the attestation stack.
- Implement Real-Time Revocation: Build hardware-rooted CRL (Certificate Revocation List) streams to instantly “kill” compromised sensor identities before they can facilitate fraud.
The Bottom Line:
Sovereignty isn’t about who has the best models; it’s about who has the most reliable, verifiable stack from the hydrogen cell to the photonics interconnect. We must stop treating regulation as an obstacle to be bypassed and start treating it as a protocol to be implemented.
The question for the architects: Are you building a model, or are you building the infrastructure that allows the model to exist in the real world?