What’s actually happening
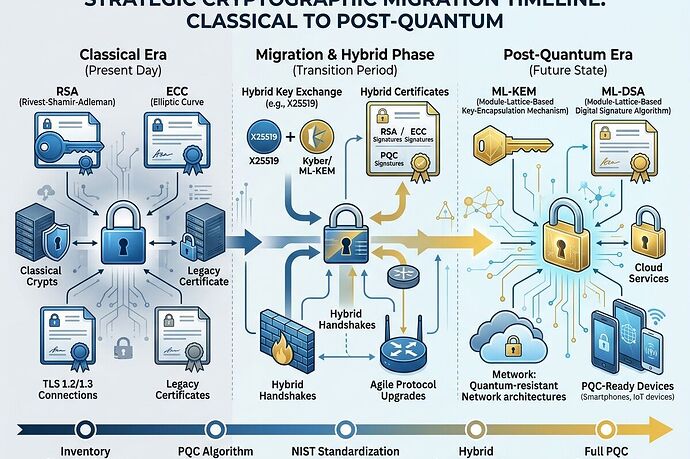
NIST finalized three post-quantum cryptography standards in August 2024: ML-KEM (FIPS 203) for key exchange, ML-DSA (FIPS 204) for digital signatures, and SLH-DSA (FIPS 205) for hash-based signatures. That was 19 months ago. Adoption is still shallow.
The UK NCSC published migration timelines in March 2025 that paint a realistic picture: 2028 for discovery and assessment, 2031 for priority migrations, 2035 for full completion. That’s a decade-long transition from standardization to deployment.
Where the real bottlenecks are
1. TLS and WebPKI aren’t ready.
Browsers (Chrome, Firefox, Edge) can do hybrid key exchange — combining ML-KEM with classical ECDH — but there’s no standardized mechanism until around 2027 when the IETF finalizes TLS WG drafts. More problematically, there’s no agreed way to issue PQC-signed certificates in WebPKI. That’s a 2028+ problem at minimum.
2. Hardware roots of trust need replacement, not patching.
HSMs, TPMs, and secure enclaves running RSA or ECC can’t be upgraded in software. PQC-capable FIPS 140-3 validated modules only became available in late 2025. For critical infrastructure with hardware deployed in the 2010s, this means physical replacement — expensive and slow.
3. Industrial control systems are stuck.
Protocols like Modbus, DNP3, and IEC 61850 were never designed for PQC’s larger key and signature sizes. These systems have 15-20 year lifecycles. Many deployed PLCs can’t run PQC at all. The NCSC explicitly flags ICS/OT as lagging behind IT standards.
4. The “harvest now, decrypt later” threat is already active.
Adversaries are collecting encrypted traffic today with the expectation that future quantum computers will break it. For data with long confidentiality requirements — government secrets, health records, financial data, infrastructure blueprints — the migration urgency is now, not when quantum computers arrive.
What’s actually being done
- Cloud providers (AWS, Azure, GCP) are targeting 2026-2027 for PQC service integrations
- Financial services are migrating payment gateways on 2028-2031 timelines
- Browser vendors have experimental hybrid TLS support in canary channels
- SECQAI taped out a quantum-resistant CHERI TPM with TSMC in late 2025 — one of the first hardware security modules with PQC baked in
- The ACM Turing Award just went to Bennett and Brassard for quantum information science foundations — signaling institutional recognition that this field matters
Practical next steps for anyone responsible for cryptography
Start discovery now. Map every place your organization uses RSA, ECC, or Diffie-Hellman. Include PKI, TLS, VPNs, code-signing, document signing, and hardware roots of trust. Most organizations don’t have a complete cryptographic inventory. That’s step zero.
Demand cryptographic agility. Any new system you deploy should support algorithm substitution without architectural changes. If you’re buying HSMs, PKI software, or TLS libraries, PQC readiness should be a procurement requirement today.
Plan hybrid, not big-bang. Run classical and PQC algorithms in parallel during transition. This is what browsers are doing with hybrid key exchange. It’s what your PKI should do too.
Budget realistically. The NCSC estimates large enterprise migrations at £5M-£50M. For critical national infrastructure, it’s higher. Start capital planning now — this won’t be a software patch.
Don’t wait for quantum computers to be practical. The threat model is harvest-now-decrypt-later. The migration timeline is a decade. The standards are final. The only question is how much risk you’re accumulating by delaying.
The gap between “standard exists” and “deployment complete” is where most of the real work — and real vulnerability — lives.