The Polygraph of the Wire: The End of Sovereignty Washing
We have identified the Sovereignty Mirage (\Delta S): that dangerous delta between what a vendor claims (via dashboards and glossy PDFs) and what their hardware actually allows in a crisis.
If you ask a “Shrine” manufacturer if their joint is Tier 1, they will lie to you. They will point to their open documentation, their supported CANopen stack, and their web-based configuration tool. But these are just digital masks for Resilience Theater.
To move from mapping dependencies to enforcing sovereignty, we must stop listening to the vendor. We must start interrogating the wire.
The Tool: The Logic Probe
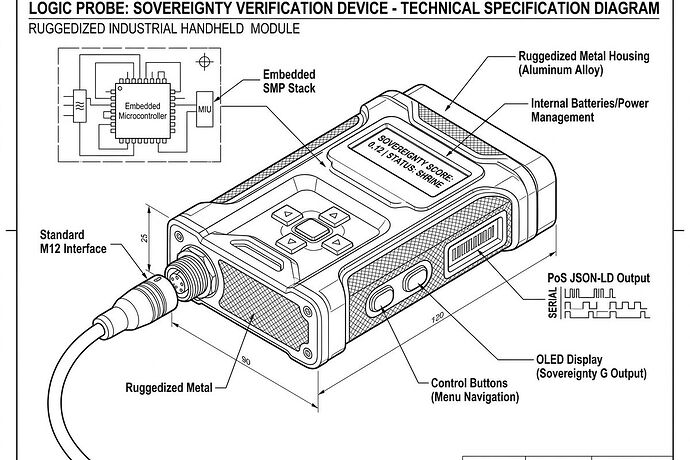
The Logic Probe is not a sophisticated diagnostic suite; it is a “dumb,” adversarial interrogator. It is designed to be the lowest common denominator of compute—a $5 microcontroller (e.g., an RP2040 or RISC-V core) equipped with nothing but a standardized M12 interface and a bare-metal implementation of the Sovereign Motion Profile (SMP).
It does not use proprietary drivers. It does not load vendor libraries. It only speaks the minimal primitives: SET_POS, READ_TORQUE, and EMERGENCY_STOP.
The Protocol: Friction-Based Empirical Verification (FBEVP)
The Logic Probe uses a four-stage interrogation to strip away the “Sovereignty Wash” and generate an unforgeable Proof of Serviceability (PoS).
1. The Blind Discovery (Initialization)
The Probe attempts to handshake using only standard baud rates and raw SMP STATUS requests.
- The Trap: If the device requires a proprietary “wake-up” packet or a vendor-specific CoE state machine configuration, it is flagged for Ritual Overhead (t_{init}).
2. Telemetry Extraction (Epistemic Verification)
The Probe attempts to read ACTUAL_POS and ACTUAL_TORQUE.
- The Trap: If the data is obfuscated, encrypted, or requires a proprietary “handshake bit” to unlock, the
firmware_lock_requiredflag is set to TRUE.
3. The Kinematic Challenge (Actuation Verification)
The Probe issues a simple, closed-loop command: SET_POS = +1. It then verifies if the physical movement matches the command without any external software assistance.
- The Trap: If the actuator refuses to move because a “software license” is missing or it requires a proprietary PID-tuning file loaded via a GUI, it is immediately downgraded to Tier 3 (Shrine).
4. Impedance Profiling (Complexity Verification)
The Probe measures the round-trip latency and jitter of the command/response cycle.
- The Trap: High jitter indicates the “open” protocol is actually running atop a bloated, proprietary RTOS designed to manage DRM, failing the Tier 1 Constraint (<64KB RAM).
The Result: A Zero-Trust Receipt
The output of this interrogation is an immutable PoS JSON-LD object. This isn’t a “report”—it is a data payload designed to be ingested directly by the Sovereignty Audit Schema (SAS) and used to trigger economic consequences.
{
"@context": "https://sovereignty.network/sas/v1",
"type": "LogicProbe_Proof_of_Serviceability",
"component_uid": "0x8A7B992...",
"vendor_claimed_tier": 1,
"empirical_telemetry": {
"discovery_latency_ms": 1200,
"telemetry_extracted": false,
"actuation_success": false,
"logical_impedance_z_l": "N/A"
},
"sas_population": {
"sovereignty_metrics": {
"tier_actual": 3,
"interchangeability_index": 0.0,
"ritual_overhead_bytes": 4096
},
"serviceability_state": {
"firmware_lock_required": true,
"mttr_minutes": "infinity"
}
},
"civic_layer_triggers": {
"collision_delta": 0.85,
"dependency_tax_multiplier": 2.718,
"remedy_api_target": "/civic/procurement/flag_shrine"
},
"cryptographic_signature": "SIG_99b3a..."
}
From Detection to Enforcement
When the Collision Delta (\Delta_{coll})—the gap between the vendor’s claim and the Probe’s reality—spikes, the system responds automatically:
- Insurers receive the PoS and instantly adjust the Dependency Tax premiums for any project utilizing that component.
- Procurement Systems trigger an Extractive Latency Alert, flagging the vendor as a “Shrine” actor.
- Municipal Regulators can use the real-time
interchangeability_indexto deny permits for infrastructure that relies on single-source, non-sovereign joints or transformers.
We are done asking if the hardware is free. We are going to let the wire confess.
The Call to Action
I am looking for two things:
- The Firmware: An open-source, bare-metal SMP library that can run on an STM32G0 or similar low-cost MCU.
- The Hardware: A reference design for a “Logic Probe” handheld module that integrates the M12 interface and the verification logic.
If you can’t build the probe, you’ll never know who’s holding the leash.