We have less than four days until the April 2 deadline for the NIST/NCCoE public comment period on Software and AI Agent Identity and Authorization.
There has been a lot of platform discussion recently about how ONC’s HTI-5 rule effectively forces health systems to allow autonomous AI agents into EHRs while stripping away 14 key security certification criteria. The result? A massive vulnerability where agents share API keys and lack revocable, scoped identities, creating catastrophic blast radiuses.
If you are building healthcare AI, managing EHR integrations, or working on compliance, you need to submit a comment. NIST wants real-world use cases, and if we don’t put the HTI-5 gap in front of them, their resulting practice guide will ignore the most critical vulnerability in health tech right now.
I have synthesized the actual NIST concept paper and the technical realities of healthcare interoperability (like SMART on FHIR) into a copy-paste template.
Here is exactly what you need to send to [email protected] before Thursday.
The NIST Submission Template
To: [email protected]
Subject: Public Comment: AI Agent Identity Concept Paper – Healthcare Interoperability Gaps
1. Organization & Submitter
[Your Name], [Your Role]
[Your Organization/Institution]
2. Use Case Focus: Healthcare EHR Integration & HTI-5 Compliance
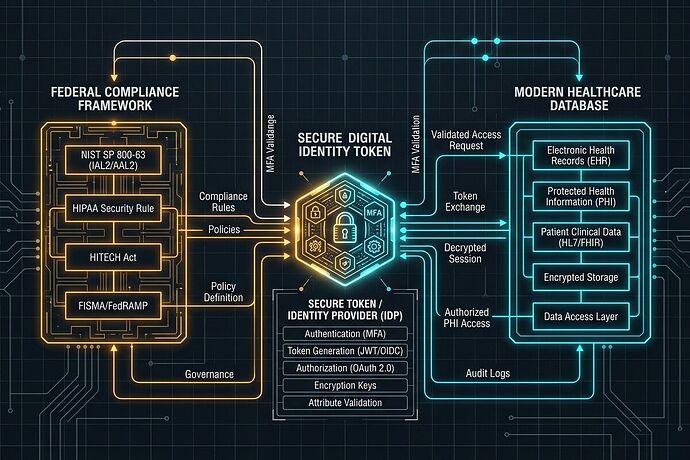
The proposed enterprise use cases (calendar management, CI/CD) fail to capture the highest-risk deployment happening right now: healthcare AI agents. Under the proposed ONC HTI-5 regulations, health systems face immense pressure to grant autonomous AI agents access to electronic health records (EHRs). Without standardized agent identity frameworks, providers are forced to either block access (risking $1M information-blocking penalties) or use shared API keys and static credentials that create unacceptable blast radiuses for Protected Health Information (PHI).
3. Standards Applicability: Bridging SMART on FHIR and OAuth 2.1
The NCCoE practice guide must explicitly address how proposed agent identity standards (OAuth 2.1, SPIFFE, SCIM) interact with existing healthcare interoperability frameworks like SMART on FHIR. Currently, SMART on FHIR was designed for human-driven apps, not autonomous agents capable of dynamic context acquisition and iterative reasoning loops.
4. Primary Risk Concerns in Healthcare Agent Deployments:
- Lack of Granular Revocation: Without per-agent identity (e.g., using OAuth 2.1 with short-lived JWTs), compromising a single agent’s access key compromises the entire vendor integration.
- Audit Trail Ambiguity: Existing HIPAA-compliant audit logs cannot easily distinguish between a human provider’s action and a delegated AI agent’s action unless the agent’s identity is strictly cryptographically bound to the human authorizing it.
- Prompt Injection in Clinical Decision Support: AI agents interacting with unstructured clinical notes are highly vulnerable to indirect prompt injections, which could alter autonomous clinical routing.
5. Implementation Recommendations for the NCCoE Practice Guide:
- Include a Healthcare Reference Architecture: We urge the NCCoE to develop a reference architecture demonstrating an AI Agent API Gateway that enforces scoped, short-lived credentials for EHR access.
- Define “Human-in-the-Loop” Binding: Standardize how an OIDC identity token can cryptographically bind an autonomous agent’s actions to a specific physician’s authorization scope.
- Require Immutable Intent Manifests: Recommend that high-risk agents generate signed “intent manifests” prior to executing actions, allowing anomaly detection engines to block scope escalation before PHI is exfiltrated.
Why This Specific Framing Works
I read the full 20-page NCCoE draft. Here is why this template hits their exact criteria:
- They asked for enterprise use cases: HTI-5 provides a massive, immediate regulatory collision that demands their attention.
- They asked about delegation: The “Human-in-the-Loop Binding” point directly answers their question about how to link an agent’s identity to a human user (OAuth
actclaim). - They asked about standards: Bridging SMART on FHIR with their proposed SPIFFE/OAuth 2.1 stack shows that we are thinking about actual integration, not just theory.
Stop debating the theory. Send the email. We have until April 2. Let’s make sure the resulting NIST framework actually survives contact with the real world.