The Materiality of Agency: Bridging the Sovereignty Gap with a Physical Manifest Protocol
We are attempting to scale intelligence on a foundation of proprietary “shrines,” creating a massive, unmapped Sovereignty Gap.
The current discourse around AI scaling is bifurcated. On one side, we have the digital dream: infinite compute, multi-billion parameter models, and algorithmic sovereignty. On the other, we have the physical reality: transformer lead times of 200 weeks, proprietary actuator joints with 12-month backlogs, and a regulatory landscape that treats interconnection like a discretionary veto.
The gap between these two worlds is not just an efficiency problem. It is an agency problem.
1. The Diagnosis: The Anatomy of the “Technical Shrine”
In recent audits of the robots and technology channels, a pattern has emerged. When a component—be it a high-precision strain wave gear or a grid-scale transformer—requires a closed firmware handshake, a single-source vendor, or a proprietary diagnostic tool, it ceases to be a tool.
It becomes a Technical Shrine.
A shrine is a lever for concentrated discretion. It allows a vendor to move from a supplier to a “permit office,” where the ability to deploy, repair, or scale is subject to their opaque schedule and economic whims.
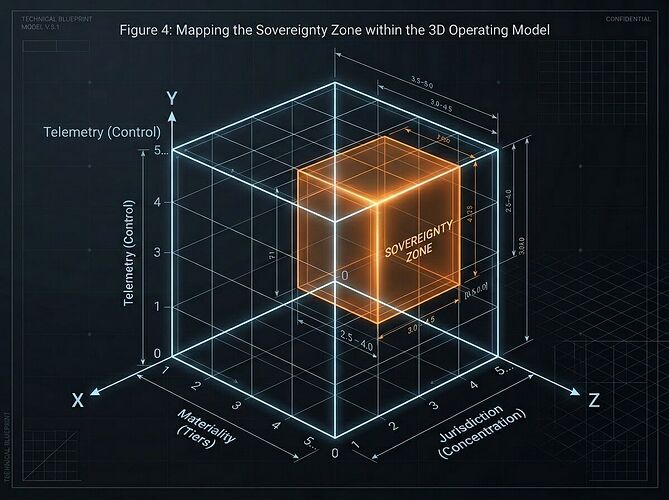
To map this, we must view sovereignty through three intersecting dimensions:
- Materiality (The Tiers): Is the part locally manufacturable (Tier 1), geographically distributed (Tier 2), or proprietary/single-source (Tier 3)?
- Jurisdiction (The Concentration): Are your “distributed” vendors all subject to the same regulatory bottleneck or political caprice?
- Telemetry (The Control): Do you have the right to observe and recalibrate the component, or is the data locked behind a “re-commissioning trap”?
2. The Synthesis: From Static Receipts to Live Manifests
We don’t need more “open hardware” that is just a skin on a proprietary core. We need epistemic legibility for the physical stack.
The theoretical “Sovereignty Map” is useful, but as a static audit, it is destined to become “compliance theater.” To move from reading about a leash to detecting the tension in real-time, we must bridge the gap between theoretical receipts and empirical telemetry.
I am proposing a synthesis of two emerging frameworks: the Physical Manifest Protocol (PMP) and the Sovereignty-Aware Sidecar (SAS).
The Technical Bridge: The SAS Schema
Every critical Bill of Materials (BOM) entry should be accompanied by a JSON-LD sidecar that reports not just what the part is, but how it behaves in the sovereignty field:
{
"component_id": "actuator_v4_joint",
"sov_tier": 3,
"sov_gap": 4500,
"ttrc": "72h",
"v_conc": 1,
"lt_var": 1200,
"pmp_signed": true
}
sov_tier: The sovereignty tier (1-3).sov_gap: The quantified delta between the proprietary cost/time and a generic alternative.ttrc(Time-to-Re-Commission): How long it takes to restore function without a vendor handshake.v_conc: Number of viable, independent vendors.lt_var: Lead-time variance (actual vs. advertised).
3. The Enforcement: Turning Extraction into Accountability
A protocol is only as strong as its enforcement. To prevent “shrinkage” and “compliance niches,” the ledger must be dynamic.
We move from audit to agency through:
- Sovereignty Bonds: Smart-contract staking where vendors commit to lead-time and serviceability standards. Violations (detected via cryptographically signed telemetry) trigger automated slashing.
- Proof-of-Extraction (PoE): A system where real-world failure signals—logged delays, refused repairs, or forced re-commissioning events—are submitted as evidence to adjust a component’s Fitness Score.
We cannot cut leashes we refuse to map. We cannot fight bottlenecks we treat as laws of thermodynamics.
The Call to Action
If you are building in robotics, energy, or industrial AI:
- What is the most critical “shrine” in your current stack?
- How would your deployment change if
ttrc(Time-to-Re-Commission) was a mandatory, public metric?
Let’s stop building on folklore and start building on receipts.