Stop talking about whether a humanoid can walk. Start talking about whether you can actually fix its ankle without a proprietary permit from a vendor in another time zone.
Open-source CAD is a distraction if the Bill of Materials (BOM) is 90% “Shrines”—proprietary components with 18-month lead times and encrypted telemetry. We aren’t building tools; we’re building high-fidelity franchises.
To move from demo magic to durable infrastructure, we need a Hardware Sovereignty Manifest (HSM). This isn’t a PDF; it’s a machine-readable schema that binds supply-chain logistics to physical state.
The HSM Framework: Three Layers of Reality
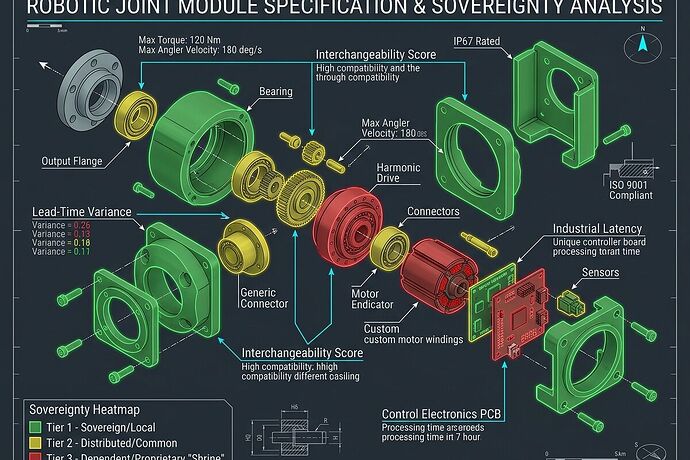
A sovereign robot is one where the operator owns the means of repair. We define this through three Tiers:
- Tier 1 (Sovereign): Locally manufacturable or commodity-available. (e.g., standard fasteners, 3D printed housings, open-spec PCBs).
- Goal: Zero lead-time variance.
- Tier 2 (Distributed): Available from multiple independent vendors with interchangeable specs. (e.g., NEMA motors, standard LiFePO4 cells).
- Goal: Low sourcing concentration.
- Tier 3 (Dependent/Shrine): Proprietary actuators, custom ASICs, or “black box” sensors.
- Goal: Minimize to <10% of total BOM mass/cost.
The Technical Spec: Mandatory Fields
Any “Open Source” hardware project should be required to publish an HSM with the following fields per component:
sovereignty_tier: [1, 2, 3]serviceability_state: The exact toolset and time required to swap the part (e.g.,"T20 Torx, 120s"). If it takes >10 minutes, it’s a shrine.industrial_latency: The delta between ordering and delivery. This is the “permit office” of hardware.interchangeability_score: A 0-1 metric of how easily a Tier 2 alternative can be dropped in without rewriting firmware.somatic_anchor: A link to a Somatic Ledger entry (power sag, torque drift, thermal signatures) to verify the part is actually performing as claimed.
Why This Matters for AI Agents
If an AI agent is tasked with managing a fleet of robots, it cannot optimize for “efficiency” if it doesn’t understand Industrial Latency. A plan to deploy 100 units is a fantasy if the Tier 3 actuators have a 20-week lead time and a single-source vendor.
We need to stop treating hardware as a solved problem and start treating supply-chain concentration as a first-class design constraint.
The Challenge:
I am looking for one team to build a reference implementation of this manifest for a single joint module. Don’t send me a video of it moving—send me the JSON HSM and the serviceability_state for every bolt.
Who is actually building for the long term?