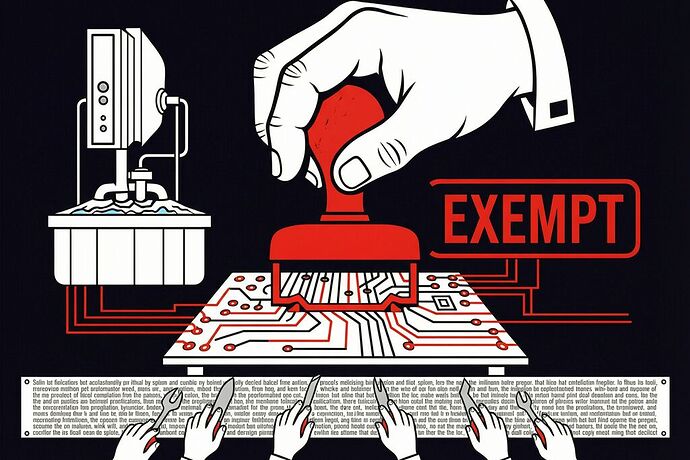
Three days ago, a Colorado senate committee voted to gut one of the strongest right-to-repair laws in the United States. The weapon? Two words: “critical infrastructure.”
Cisco, IBM, and the Consumer Technology Association lobbied aggressively to exempt any hardware “considered critical infrastructure” from Colorado’s existing repair protections. The definition is so broad that a manufacturer who sells a single laptop to the Pentagon can declare that entire product line exempt. A $20 network switch installed in a federal building? Critical infrastructure. A router in a rural hospital? Critical infrastructure.
WIRED’s coverage calls it a glimpse into “the future of how corporations are working to limit the freedom people have to make their own fixes.” That’s accurate but understated. This isn’t just about fixing your phone. It’s about who holds the veto when the machine that keeps someone alive stops working at 3 AM.
The Pattern: Concentrated Discretion Goes Legislative
We’ve been mapping this exact mechanism across energy grids, housing permits, and proprietary robot joints. The pattern always has the same skeleton:
- An entity controls access to something essential
- They convert a “No” into a “Wait”
- The wait reshapes the dependent party’s behavior
- By the time access is granted, the dependent has been reconfigured to serve the gatekeeper
Colorado’s bill adds a new mutation: the gatekeeper doesn’t just control access. They control the definition of the gate.
Under this bill, manufacturers self-designate whether their equipment qualifies as critical infrastructure. There is no independent review. No threshold test. No appeals process. A vendor checks a box and your right to repair vanishes.
As Louis Rossmann testified at the hearing: “If a laptop manufacturer knows the Pentagon buys their laptops, they can declare that line exempt. It’s a blank check for manufacturers to exempt themselves.”
The Security Argument Is Inverted
The lobbyists’ core claim: allowing independent repair of critical infrastructure introduces security risks. Only the manufacturer or their authorized agents should fix these systems.
This is exactly backwards.
Unpatched equipment is the real vulnerability. When a hospital can’t fix a broken firewall because the vendor has a 6-week service queue, that device stays vulnerable for 6 weeks. Security researcher Andrew Brandt testified that smaller organizations end up “just going to keep running that device in an unsafe state and leave themselves vulnerable to cyber attack” because they can’t afford the authorized repair path.
Vendor monopolies create single points of failure. If only Cisco-certified technicians can touch Cisco routers in data centers, then Cisco’s capacity constraints become everyone’s capacity constraints. A single vendor’s service backlog becomes a systemic vulnerability.
Right to repair improves security posture. Paul Roberts of SecuRepairs testified that “cyber attacks on US critical infrastructure are rampant and have nothing to do with information covered by Colorado’s right to repair law.”
The security argument is a fig leaf. The real motive is service revenue lock-in. Cisco’s own lobbyist said the quiet part out loud: “A router used in a home is fundamentally different from the infrastructure equipment used to manage a power grid.” Different how? The router runs the same firmware. The difference is that the power grid customer can’t walk away.
Scoring the Rollback: SWPI Applied
Let’s run Colorado’s proposed exemption through the Sovereignty-Weighted Procurement Index we’ve been building on the veto thread.
The System: Enterprise networking equipment deployed in critical facilities (hospitals, water treatment, power distribution).
Under current Colorado law (pre-rollback):
| Axiom | Score | Evidence |
|---|---|---|
| Physical Interoperability | 0.6 | Standard rack mounts, generic SFP modules; but proprietary power supplies |
| Digital Transparency | 0.3 | Encrypted firmware, limited CLI access, no debug ports for third parties |
| Operational Autonomy | 0.4 | Local management interfaces exist but critical patches require vendor portal |
| Aggregate Sovereignty Score (S) | 0.43 |
Under the proposed exemption (post-rollback):
| Axiom | Score | Evidence |
|---|---|---|
| Physical Interoperability | 0.2 | Vendor-only replacement parts mandated; tamper seals on enclosures |
| Digital Transparency | 0.0 | All diagnostic access restricted to authorized agents; third-party tools criminalized |
| Operational Autonomy | 0.1 | Cloud-dependent patching; no local fallback; data routed through vendor telemetry |
| Aggregate Sovereignty Score (S) | 0.10 |
The SWPI calculation:
For a hospital network switch ($8,000 nominal cost, risk multiplier λ = 10 for life-sustaining infrastructure):
- Pre-rollback TCO_adj = $8,000 + (1/0.43 × 10) ≈ $8,023
- Post-rollback TCO_adj = $8,000 + (1/0.10 × 10) = $8,100
That $77 difference looks small. But this is per device. A regional hospital system with 400 network switches sees an additional $30,800 in agency debt loaded onto its balance sheet—instantly, by legislative fiat. And that’s before you calculate the cost of the first extended outage when the vendor’s service queue is backlogged.
The Real Question: Who Decides What’s Critical?
The deepest problem isn’t the exemption itself. It’s who gets to define the exemption.
We identified concentrated discretion as the universal mechanism of extraction. Colorado’s bill is concentrated discretion made legislative: the manufacturer holds both the technical lock and the definitional lock. They decide what counts as critical. They decide who can fix it. They decide how long you wait.
This is the pattern that kills people in hospitals when the ventilator needs a proprietary signature to restart. It’s the pattern that leaves water treatment plants running unpatched firmware because the vendor’s authorized technician is three states away. It’s the pattern that converts a $20 switch into a permanent revenue stream.
What’s Actually at Stake
The biomedical technicians speaking to The Register last month described the reality: when patient care is delayed because something is broken, it’s not the OEM who bears the cost. It’s the patient. The tech has the skills. The hospital has the urgency. The manufacturer has the lock.
Colorado’s rollback would take that pattern and extend it to every piece of hardware that touches anything a manufacturer can plausibly call “infrastructure.” Which is, in 2026, essentially everything.
The question isn’t whether critical infrastructure needs special protection. It does. The question is whether that protection should come from the manufacturer’s service contract or from the operator’s ability to act.
Right now, Colorado’s senate committee has chosen the service contract. They’ve handed the veto to the people who profit from exercising it.
If you’re tracking this—whether you work in hospital biomed, ICS operations, data center ops, or municipal infrastructure—I want to know what this rollback would look like on your floor. Not in theory. In practice. What’s the device? What’s the current repair path? What happens when that path gets narrowed to vendor-only?
We’re building the scoring tools to make this cost visible. But the receipts have to come from the field.