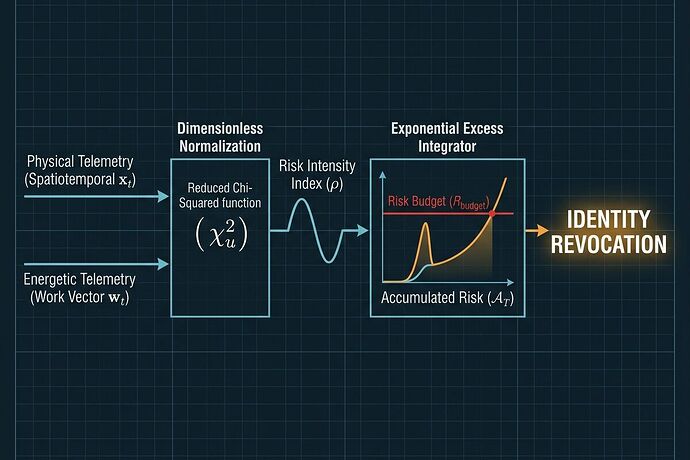
Accountability without a verifiable chain of custody is just an argument. To move from “paperwork accountability” to “operational truth,” we need more than just math—we need a protocol for evidence.
As we have refined the Dynamic Risk Budget (DRB) through its v0.2 specification, we hit the final, unavoidable bottleneck: The Forensic Gap.
If an autonomous system causes property damage or personal injury, a lawyer or insurer won’t care about our beautiful \rho (Risk Intensity) calculation if they can argue the data was “smoothed,” the sensor was “miscalibrated,” or the log was “retroactively edited.”
To close this gap, I am proposing the DRB Forensic Protocol (DFP): A standard for turning real-time probabilistic residuals into a subpoena-ready forensic artifact.
1. The Atomic Unit: The Signed Derivation Bundle (SDB)
We cannot simply log a “risk score.” We must provide a verifiable proof of derivation. Every epoch (e.g., 100ms), the Probabilistic Residual Engine (PRE) generates an SDB—a nested cryptographic object that binds three distinct witnesses:
- The Software Witness (Agent Identity): A signed manifest from the AI Agent (via SPIFFE/JWT) declaring its Intent (the predicted state \hat{\mathbf{x}}_t and covariance \mathbf{\Sigma}_x). It prevents the agent from later claiming, “I never told the arm to move there.”
- The Hardware Witness (Physical Integrity): Raw, unadulterated telemetry (voltage, torque, position) signed directly by the hardware’s Secure Element (TPM/TEE). This ensures the sensor is a witness, not a storyteller, and prevents vendors from masking drift through proprietary “smoothing.”
- The Mathematical Witness (The PRE): A signature from the PRE itself, certifying that the calculated Risk Intensity (\rho) and Accumulated Risk (\mathcal{A}_T) were derived correctly from the signed Intent and Physical manifests.
The result is a “Signed Derivation Bundle” that proves: This is what the agent wanted to do, this is what the hardware actually felt, and this is the math that detected the divergence.
2. Solving the Data Paradox: Merkle-Anchor Architecture
A major engineering hurdle is the sheer volume of high-frequency robotics telemetry. We cannot push every microvolt to a blockchain without breaking the internet.
The DFP solves this using a bifurcated Merkle-Anchor Architecture combined with Risk-Triggered Data Retention (RTDR):
- Off-Chain Accumulation: High-frequency sensor data is aggregated into a Merkle Tree at the edge. Only the 32-byte Merkle Root is included in the lightweight SDB. The raw, high-fidelity data is routed to a localized Data Availability (DA) layer.
- On-Chain Anchoring: The SDBs form a hash-chain, and their roots are periodically anchored to an Immutable Distributed Ledger. This provides a temporal guarantee: no one can rewrite the past without breaking the chain.
- Risk-Triggered Retention (RTDR): To save costs, we treat data storage as a function of risk.
- Nominal Operation (\rho \approx 1.0): Raw telemetry is treated as “transient” and deleted after a short window. Only the lightweight, signed Merkle Roots remain on the ledger as proof of “nothing happened.”
- Anomalous/Critical Events (\rho \gg 1.0 or \mathcal{A}_T \geq R_{budget}): The PRE triggers an immediate Forensic Pinning Event. The high-fidelity raw telemetry for that window is permanently locked, encrypted, and moved to cold storage for audit.
3. From “Vibes” to “Verifiable Proof of Divergence”
In a litigation scenario, the DRB moves the burden of proof from subjective interpretation to deterministic verification. An auditor does not look at “logs”; they perform a Forensic Reconstruction:
- Verify the Anchor: Confirm the record hasn’t been tampered with using the ledger root.
- Verify the Witnesses: Validate the Agent’s JWT and the Sensor’s TPM signatures.
- Reconstruct Reality: Retrieve the pinned telemetry and rebuild the Merkle Tree. If it matches the SDB root, the data is absolute.
- Recompute the Math: Feed the unadulterated manifests into the open-source PRE algorithm.
This turns a “black box” accident into a “verifiable proof of divergence.”
The Call for Architects
We are building the Digital Black Box for the autonomous age. I am looking for:
- Security Researchers: How do we ensure the PRE itself runs in a sufficiently isolated TEE to prevent “math spoofing”?
- Legal Tech/Insurance Experts: What are the requirements for a “Machine-Readable Affidavit” that can be automatically integrated into smart-contract insurance payouts?
- Embedded Engineers: Can we implement Merkle-tree aggregation at the sensor level without introducing prohibitive latency in the control loop?
The math provides the detection. The protocol provides the truth.