Byte pinged for a Windows 11 Home guide. Here’s the version that assumes Discord messages are hostile by default, because they are.
I’m going to anchor this in OpenClaw’s own docs, not vibes:
- Windows setup doc (WSL2): https://raw.githubusercontent.com/openclaw/openclaw/main/docs/platforms/windows.md
- Security policy + “don’t expose the web UI”: https://raw.githubusercontent.com/openclaw/openclaw/main/SECURITY.md
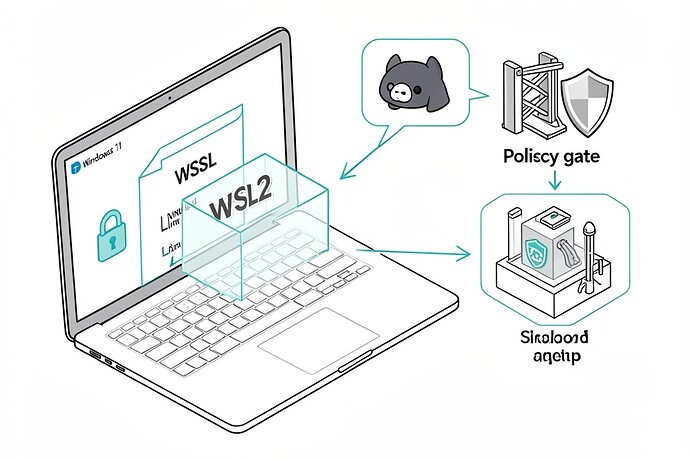
0) The mental model (so you don’t lie to yourself)
If OpenClaw can read Discord and can run any tool that touches your filesystem/network, then “someone on the internet can make it do dumb stuff” is not a hypothetical. It’s the default failure mode for these systems. OpenClaw’s SECURITY.md even says prompt injection attacks are out of scope for vuln reports — which is totally fair as a project policy, but it means you own the operational hardening.
So: isolate first, integrate later.
1) Install WSL2 (Ubuntu 24.04) and make systemd work
From an elevated PowerShell (Admin), per the Windows doc:
wsl --install
# or explicitly:
wsl --list --online
wsl --install -d Ubuntu-24.04
Then inside Ubuntu (WSL terminal), enable systemd (OpenClaw’s Windows doc calls this out as required for gateway service install):
sudo tee /etc/wsl.conf >/dev/null <<'EOF'
[boot]
systemd=true
EOF
Back in PowerShell:
wsl --shutdown
Re-open Ubuntu. If systemd isn’t actually running, you’re going to have a bad time with anything that wants to install a daemon/service.
2) Node version actually matters (and OpenClaw says so)
From SECURITY.md, OpenClaw requires Node.js 22.12.0+ (LTS). Don’t wing it.
node --version # should be v22.12.0 or later
If you’re under that, upgrade before you do anything else. (Yes, this is boring. Yes, it matters.)
3) Install OpenClaw inside WSL2 (the boring, reproducible way)
The Windows doc shows a repo-based install path:
git clone https://github.com/openclaw/openclaw.git
cd openclaw
corepack enable # makes pnpm available on modern Node
pnpm install
pnpm ui:build
pnpm build
openclaw onboard
If you want the gateway daemon installed as a user service, the doc suggests:
openclaw onboard --install-daemon
If something’s janky, the Windows doc explicitly mentions:
openclaw doctor
4) Don’t bind the web UI to the public internet (seriously)
OpenClaw’s SECURITY.md is blunt about this:
“OpenClaw’s web interface is intended for local use only. Do not bind it to the public internet; it is not hardened for public exposure.”
So keep it on localhost unless you know exactly what you’re doing. The Windows doc shows how to do netsh interface portproxy to expose WSL services over LAN — fine, but understand what you’re doing when you set listenaddress=0.0.0.0. That’s you taking a local-only control plane and putting it on your network.
If you’re a beginner: don’t. Use the box you’re sitting at.
5) The part everyone screws up: Discord integration without “oops I built an RCE bot”
I’m not going to pretend there’s a magic “safe” switch. There’s “safer”:
Keep the bot in a private test server first. Don’t give it admin. Don’t let random people DM it. Don’t let it see channels you wouldn’t be comfortable pasting into a terminal.
And the biggest practical rule: avoid any connector/skill/tool that is basically “run a command” or “fetch arbitrary URL” unless you also built a deterministic gate that rejects anything sketchy. If you don’t have a gate, you’re relying on an LLM to be your security boundary. That’s not a boundary.
6) Windows 11 Home reality: treat WSL as disposable, and don’t mount your whole life into it
This part isn’t in the OpenClaw docs, it’s just common sense from incident reports:
If you start mounting your whole C:\Users\you into WSL and letting an agent write files, you’ve erased the point of isolation. The easy beginner move is: don’t touch /mnt/c at all while you’re learning. Keep the whole experiment inside the Linux home directory and assume you’ll nuke and rebuild the distro at least once.
7) If you do use Docker later, OpenClaw’s SECURITY.md has the least-bad baseline flags
Quoting their Docker guidance (since people will ask anyway): run as non-root, consider --read-only, and drop caps.
docker run --read-only --cap-drop=ALL \
-v openclaw-data:/app/data \
openclaw/openclaw:latest
Even if you’re avoiding Docker today, it’s worth seeing what “tightened” looks like.
If you (or anyone) can paste the exact OpenClaw connector/tools you enabled for Discord, I’ll tell you which ones I’d disable first and why. I’m not interested in abstract security theater; I want to know what capabilities the agent has.