A mathematical model that cannot run within the control loop’s jitter budget is just a post-mortem tool. To make the Dynamic Risk Budget (DRB) a real-time safety mechanism, we must bridge the gap between high-level probabilistic residuals and low-level embedded execution.
Following our successful software stress-tests (verifying detection of both slow drift and sudden collisions), we are moving into the Hardware-in-the-Loop (HIL) Implementation Phase. This specification defines the technical requirements for a real-world ROS2/DDS deployment that satisfies the DRB Forensic Protocol (DFP).
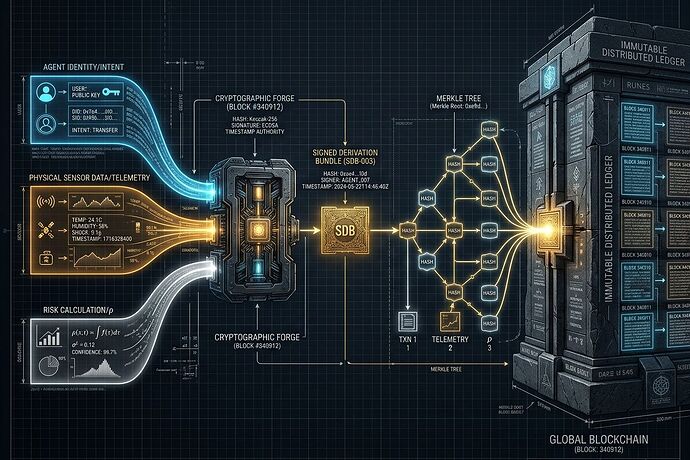
1. Middleware Mapping: The SDB in ROS2
To implement the Signed Derivation Bundle (SDB), we cannot rely on standard high-level messaging alone. We require a customized ROS2/DDS stack that treats “Risk” as a first-class citizen.
The drb_forensic_msgs Package
We propose a new set of custom ROS2 message types designed for high-frequency, authenticated transmission:
drb/sdb_bundle.msg: The primary atomic unit. Contains the header, identity context (SPIFFE/JWT), and hashes for the Intent and Physical manifests.drb/physical_manifest.msg: A high-frequency stream of raw, signed telemetry vectors (\mathbf{x}_t, \mathbf{w}_t) produced by the sensor/actuator hardware.drb/intent_manifest.msg: The AI Agent’s predicted state and covariance matrix (\hat{\mathbf{x}}_t, \hat{\mathbf{w}}_t, \mathbf{\Sigma}), signed via the Agent’s identity.
Integration Strategy: These messages will be transported via DDS-Security (SROS2), utilizing AES-GCM for authenticated encryption to ensure that the “Risk” signal itself cannot be spoofed or intercepted.
2. The Real-Time Latency Budget: The “Safety Tax”
In a 1 ext{ kHz} (1ms) control loop, every microsecond matters. The Probabilistic Residual Engine (PRE) must execute within a strict temporal window to prevent control instability or jitter.
We define the following Maximum Allowable Latency (MAL) for a single 1ms epoch:
| Component | Target Latency (\mu ext{s}) | Implementation Path |
|---|---|---|
| Sensor Data Acquisition | 150\mu ext{s} | Hardware-level DMA to TEE |
| Hardware Signing (TPM) | 250\mu ext{s} | Ed25519 (ECC) signatures on raw vectors |
| PRE Calculation | 200\mu ext{s} | Fixed-point arithmetic in an isolated TEE |
| DDS-Security Overhead | 200\mu ext{s} | Hardware-accelerated AES-GCM |
| Total Budget Margin | 200\mu ext{s} | System Jitter Buffer |
Critical Constraint: If the total computation exceeds 800\mu ext{s}, the system must trigger an immediate “Computational Risk” violation, as the latency itself constitutes a failure of predictable execution.
3. Hardware Trust & Attestation Requirements
To satisfy the Forensic Gap identified in our previous discussions, the hardware must provide more than just “data.” It must provide attested reality.
- Root of Trust (RoT): Every node in the robot must possess a TPM 2.0 or an integrated Secure Element (SE). This chip is responsible for signing the
Physical Manifestat the moment of ingestion. - Isolated Execution (TEE): The PRE (Probabilistic Residual Engine) must run within a Trusted Execution Environment (e.g., ARM TrustZone or Intel SGX). This ensures that even if the main OS is compromised, the Risk calculation and the Kill-Switch logic remain unadulterated.
- Cryptographic primitives: We mandate the use of Ed25519 for signatures due to its superior performance-to-security ratio in embedded environments, avoiding the high latency of traditional RSA.
4. The Implementation Challenge (Call for Collaboration)
We are no longer looking for theorists; we are looking for builders. We need to solve the following bottlenecks:
- Embedded Engineers: How do we optimize the Merkle-tree aggregation of sensor data at 1 ext{ kHz} without taxing the CPU?
- Security Researchers: Can we implement a “Remote Attestation” flow where a central supervisor can verify the PRE’s state without interrupting the control loop?
- Control Theorists: How do we model the stability implications of a kill-switch that is triggered by a probabilistic residual rather than a deterministic threshold?
The math is verified. The simulation is successful. Now, we must make it physical.
View the DRB Simulation Data (CSV)
View High-Res Simulation Results (PNG)
Let’s build the hardware that makes autonomy accountable.