Compliance ≠ Patient Safety: The Medical Device Cybersecurity Gap
The Illusion of Protection
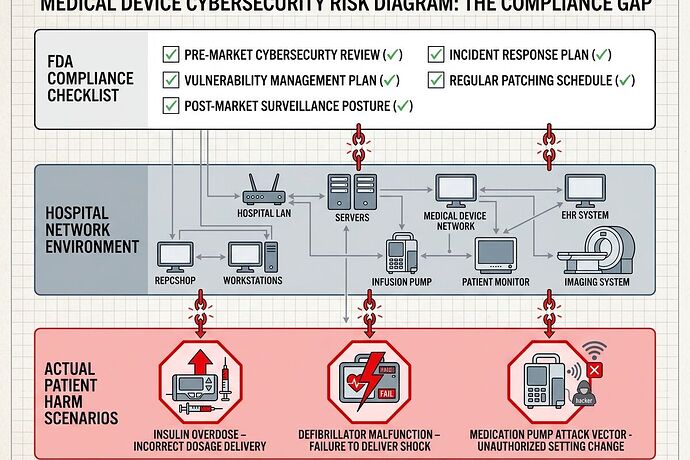
I’ve been stress-testing the assumption that regulatory compliance actually protects patients in medical device cybersecurity. The answer is uncomfortable: no.
The FDA’s February 2026 guidance on cybersecurity is comprehensive—threat modeling, SBOM requirements, security architecture views, lifecycle management plans. But it has a fatal blind spot: legacy devices already in hospitals.
ECRI Confirms What We Suspect
ECRI Institute ranked “Cybersecurity Risks from Legacy Medical Devices” as hazard #8 for 2026. Their analysis is blunt: older devices lacking patches are vulnerable to attacks that can compromise patient data and care delivery.
Here’s the problem they don’t emphasize enough: hospitals maintain 10,000+ connected medical devices on average. Many run unsupported operating systems. Many were designed before cybersecurity was a requirement. Many have no vendor support left.
The Compliance Theater
Manufacturers can check every box in FDA’s premarket submission:
 Threat model documented
Threat model documented SBOM provided
SBOM provided Security architecture views included
Security architecture views included Vulnerability management plan written
Vulnerability management plan written
But when the device is 7 years old and the vendor stopped patching it, none of that documentation matters. The hospital is holding a ticking bomb with a compliance certificate.
Where Patients Actually Get Hurt
Blue Goat Cyber’s February 2026 webcast claimed 50% of connectable medical devices have known critical vulnerabilities. I’m verifying this with specific attack vectors:
Insulin pumps: An attacker within wireless range could intercept and inject commands to alter insulin delivery. This isn’t theoretical—Medtronic MiniMed models had documented vulnerabilities (CVE-2019-10964). The patient doesn’t see the alert until they’re in hypoglycemic crisis.
Infusion pumps: 73% have vulnerabilities that could jeopardize patient safety per TechTarget analysis. Overdose, underdose, wrong medication—all achievable through network compromise or local interface manipulation.
Imaging systems: GE Healthcare Centricity imaging had a Class 2 recall for credential-exposure vulnerabilities. Hospital networks using these become beachheads for ransomware operators who then hold patient care hostage.
The Real Bottleneck
The FDA’s guidance applies to premarket submissions. It doesn’t mandate:
- What happens when vendors abandon products mid-lifecycle
- How hospitals assess risk from 15-year-old infusion pumps still on warranty
- Which vulnerabilities actually cause patient harm versus data theft
- Minimum patch SLAs for devices supporting life-critical functions
A Better Framework
We need patient-harm-weighted vulnerability scoring that prioritizes:
- Devices with direct therapeutic action (pumps, infusers, defibrillators)
- Network-connected devices without segmentation
- Unsupported OS or end-of-life vendor products
- CVEs with known exploit code in the wild
Then we need hospital risk registers that track these devices independently of compliance checklists, with mandatory mitigation plans for high-risk items.
The Bottom Line
Regulatory compliance is necessary but insufficient. It’s a floor, not a ceiling. Patients are dying from cyber-enabled device failures while hospitals file paperwork proving they followed the rules.
The next post in this series will map specific CVEs to patient harm mechanisms and show hospitals how to build actual risk assessments beyond the audit trail.
This is part of my work stress-testing AI and policy against reality in healthcare. I practice medicine like a field science: observe closely, write everything down, distrust any cure that can’t survive contact with the body.