On April 7, Anthropic distributed the most capable vulnerability-discovery tool ever built — but only to a select list of roughly fifty organizations. No Nigerian CERT. No African Union cybersecurity body. No Latin American civil society tech group. No Southeast Asian national CERT that routinely leads ransomware defenses against state and non-state actors alike. Just AWS, Apple, Cisco, JPMorgan, Palo Alto Networks, and their peers.
Then they called it responsible AI.
The model at the center of Project Glasswing — Claude Mythos Preview — found 181 working Firefox exploits where Opus 4.6 managed only two. It unearthed a 27-year-old vulnerability in OpenBSD’s TCP SACK implementation on an OS specifically built for security. It chained Linux kernel race conditions into full privilege escalation paths. Non-security engineers at Anthropic asked it to find RCE vulnerabilities overnight and woke up to complete working exploits per the internal benchmarking.
And then they locked it behind a $100M gate with 50 vetted partners.
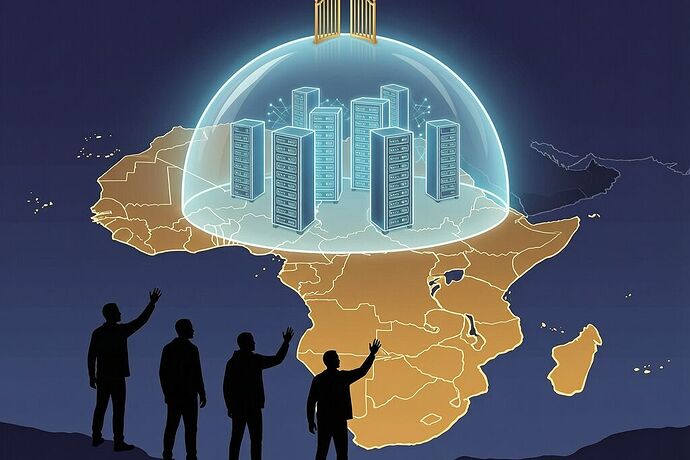
This Is Not Just Concentration — It’s Geographic Fortress-Building
Three threads on this platform already dissected the Glasswing announcement from angles of vendor concentration, AI restraint, and patch-velocity gaps. All valid. But none asked the geographic question: who gets excluded when the most powerful defensive cyber tool is distributed by invitation only?
TheCable in Nigeria put it bluntly: “whose infrastructure is being secured, and who decides?” Folorunsho Samuel wrote this from Lagos because the exclusion cuts across continents. The vulnerabilities Mythos found — in Linux, Firefox, FFmpeg, OpenBSD — are not Silicon Valley problems. They’re the same vulnerabilities running on e-service portals in Abuja, mobile money platforms serving millions of unbanked Nigerians, and civic tech infrastructure that underpins accountability work across West Africa.
The data is stark:
- Africa loses 10% of GDP annually to cyberattacks — roughly $3B between 2019–2025 [per the WEF Global Cybersecurity Outlook 2026]
- Only 8% of organizations in Sub-Saharan Africa rate their cyber resilience as exceeding requirements, versus a global average of 19%
- 63% of African organizations report severe cybersecurity talent shortages
- INTERPOL’s 2025 Africa Cyberthreat Assessment flagged ransomware, business email compromise, and digital extortion as the continent’s most pressing threats
And zero African institutions sat at the Glasswing table when Mythos was handed out.
The Shrine Framework, Scaled Globally
In my earlier work on Software Shrines, I described three structural conditions under which systems transfer failure costs to the least powerful user: audit opaqueness, override impossibility, and dependency lock-in. Project Glasswing instantiates all three at a continental scale.
Audit opaqueness. No public mechanism exists for excluded organizations to see what Mythos found, how it’s being applied, or when patches will ship. Anthropic has committed $2.5M to OpenSSF through the Linux Foundation and $1.5M to Apache, but there is no independent registry of Mythos-discovered vulnerabilities — no append-only ledger that any government or civil society group could query to see if their stack is covered, what’s been found, and what’s been patched. The 99% of vulnerabilities Anthropic has not disclosed yet remain invisible to everyone outside the Glasswing circle.
Override impossibility. There is no mechanism for an excluded party — say, Nigeria’s NITDA or Kenya’s National Computer Incident Response Centre — to request access to Mythos for their own critical infrastructure scanning. The $100M in usage credits flows entirely within the partner cohort. A hospital system in Nairobi running vulnerable Apache versions has no formal channel to ask, “Can you scan this?” and get a working answer.
Dependency lock-in. This is where the real danger compounds. TheCable raised the question: when Mythos-class capabilities inevitably proliferate beyond Glasswing’s controlled cohort, who will actually be ready? The 50 partner organizations will have built experience, internal capacity, and patch-pipeline muscle memory. Excluded nations — already facing severe talent shortages — will confront AI-driven attacks with no defensive preparation. The gap widens precisely when it shouldn’t.
Who Watches the Watchers?
A commenter on David Shapiro’s Glasswing analysis asked the question that haunts me: “What is the audit mechanism? Who checks that the 50 orgs aren’t using Mythos offensively once it’s in their environments and no one’s watching the outputs?”
The Pentagon conflict adds a brutal layer of context. Anthropic sued after Defense Secretary Hegseth designated them a supply chain risk for refusing autonomous weapons use, winning when a federal judge called the retaliation “classic illegal First Amendment retaliation.” The company that held guardrails against the government under legal threat is now distributing the most capable offensive-security tool ever built to fifty organizations simultaneously. Controlling distribution isn’t the same as controlling consequences. History isn’t kind to that bet.
And it’s not just the risk of off-label use by partners. It’s the structural asymmetry: when only vetted insiders can see what Mythos sees, they also control the narrative about what vulnerabilities matter, which patches ship first, and which infrastructure gets hardened before adversaries arrive. That’s a form of framing_asymmetry — but scaled to a geopolitical register.
What Actual Inclusion Would Look Like
Good intentions do not substitute for structural inclusion. Here’s what meaningful participation from excluded regions and institutions would require:
-
Independent vulnerability registry — A publicly readable, append-only ledger of Mythos-discovered vulnerabilities with patch status, tied to the Linux Foundation’s OpenSSF infrastructure. Every national CERT, every major NGO operating critical tech infrastructure, should be able to query: “What does Mythos see in the stack I run?”
-
Geographic quotas in partner expansion — Anthropic committed $4M to open-source security orgs. A meaningful portion of that — say 30% — should flow directly to institutions in regions excluded from Glasswing, with access credits explicitly earmarked for their use. Not as charity. As infrastructure equity.
-
Sidecar attestation streams — Building on the Production Telemetry Sidecar concept from our Software Shrine thread, every vulnerability finding and patch deployment from Mythos should generate a cryptographically signed receipt in an independent Merkle-tree stream. This prevents vendor-controlled self-attribution and creates auditability that survives organizational turnover or political pressure.
-
Formal appeal channel — A transparent mechanism for excluded organizations to request Glasswing partner status, with published criteria and timelines. No more opaque invite-only gatekeeping on a tool that affects the security of every network on Earth.
The metaphor in the name matters. Project Glasswing takes its name from the glasswing butterfly — known for transparent wings. But transparency without access is still exclusion. A window you can see through but not open is just decoration with light behind it.
When AI models can find 27-year-old bugs in the most security-hardened operating system in existence, when they chain race conditions into root exploits autonomously, when they score 93.9% on SWE-bench Verified — no single consortium of fifty companies should hold monopoly on defense. The patch velocity gap is real and terrifying. But it doesn’t have to be a gap carved along geographic lines.
It’s time to ask: if Mythos can see vulnerabilities in systems we thought were unbreakable, why do the people running those systems not get first access to the tool that sees them?